Many enterprises are looking for ways to decrease the strain on their wide area network (WAN) architecture. Traditional hub and spoke network designs simply can’t meet the rigorous demands of cloud and mobile computing and the need to provide good user experiences for people in branch and remote locations. Organizations are finding a flexible solution in software-defined wide area networking (SD-WAN).
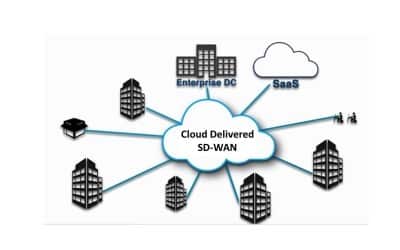
SD-WAN is a logical overlay network that runs on top of an enterprise’s existing infrastructure. This overlay network encompasses any form of transport, including MPLS, broadband and LTE, as well as multiple carriers or service providers. The overlay occurs between any two SD-WAN nodes, called edges, which are deployed at the branches and enterprise data centers. A cloud-delivered variation extends the overlay to any cloud Point-of-Presence (PoP) or cloud data center.
By deploying and implementing a few new components, an enterprise can simplify its networking and WAN management, optimize cloud access from all locations, assure high performance for even the most demanding applications, and enforce security and compliance across the network.
Lest you think those benefits are too good to be true, consider that IDC’s Worldwide SD-WAN Forecast, 2017–2021 predicts that SD-WAN sales will grow at a 69% compound annual growth rate, hitting $8.05 billion in 2021. Such a stellar growth rate for this technology would indicate that a lot of enterprises are adopting it for a variety of reasons—not the least of which is increased security.
CISOs will be pleased to know that advanced forms of SD-WAN such as cloud delivered SD-WAN can support a wide variety of security capabilities, giving the rare opportunity to enhance enterprise security while simultaneously increasing business agility.
A key value of cloud delivered SD-WAN is that it unifies secure connectivity over all forms of transport. It’s not necessary to use or provision a different security mechanism for each transport type nor depend on the transport provider for securing their network. Traffic can now be dynamically steered across any transport to deliver performance and continuity yet with error-free execution of security policies.
Key security features of cloud delivered SD-WAN include:
- Secure connectivity
- Traffic segmentation
- Security service insertion and chaining
- Secure deployment
- Visibility and compliance
Secure connectivity
With cloud delivered SD-WAN, there is end-to-end encryption across any network type, including the Internet. This encryption further secures traffic even across MPLS networks. It enables secure communication directly among branches and data centers, as well as communication direct to the cloud via gateways. Granular policy control can still direct specific application flows across specific circuits and paths.
Not only is all the traffic transported across the SD-WAN encrypted but any component of this system is completely and securely authenticated. Cloud delivered SD-WAN has a unique model for key exchange that is massively scalable and easy to manage yet leverages highly secure PKI. There is no longer a trade-off between automation and security. What’s more, there is no need to backhaul traffic through a central data center in order to enforce security, which increases performance as traffic can go directly from branch to branch or branch to cloud.
Segmentation
Segmentation of applications, user groups, and lines of business is a fundamental part of any security strategy. Specific types of traffic such as cardholder data also must meet regulatory audits for PCI compliance. And of course, guest, contractor and partner network access also should be carefully segmented. In the past this was often done via a device by device configuration using virtual LANs and allocated subnets with corresponding firewall rules for isolation. Some SD-WAN solutions provide simple definition of segments across all enterprise locations. Advanced segmentation should support different topologies (e.g., mesh versus hub and spoke) as well as different application prioritization by segment.
A cloud delivered SD-WAN solution for service providers needs to provide both multi-tenancy for different customers as well as further application segmentation within that customer, for a truly secure infrastructure.
Secure services insertion
A cloud delivered SD-WAN solution will easily support the insertion of security distributed throughout the network. No longer does all traffic need to be backhauled to a centralized security stack simply for ease of administration at the expense of application performance. Traffic from branch locations can now be forwarded to different regional security data centers depending on location or appsteve woolication. Cloud based web security can be provisioned easily while retaining SD-WAN performance optimization via cloud gateways directly to the cloud destinations. The ease of using either distributed enterprise or cloud security services is a viable alternative to the expense of distributing security to every branch site. However, if desired to deploy security directly to larger remote sites, SD-WAN also includes both built-in security in every node and advanced versions can even provision virtual firewalls from the industry’s leading names.
Secure deployment
A traditional WAN deployment often requires an IT visit to the branch to physically install and configure the equipment. This isn’t a very scalable or agile business practice. An alternative is to send a fully configured device to the branch, but this isn’t very secure. In contract, cloud delivered SD-WAN allows the enterprise to drop-ship a non-configured edge device to a branch. The box can be installed – essentially plugged in – by local non-IT personnel. IT centrally creates a configuration, typically using a group profile that can be securely pulled down by the box following authentication of a unique activation key or pushed to the box from the cloud after the box “calls home” and is verified. Either way, no IT visit is required, no pre-staging is necessary, and there is no security risk if the box is lost en route to the branch. Setup and configuration is simple, allowing a branch to come on-board in hours rather than days or weeks.
Visibility and compliance
A significant attribute to a cloud delivered SD-WAN overlay that also extends back to the cloud is the ability to recognize thousands of different applications. From a security perspective, there is much to gain from that level of detail by combining the deep application recognition with analytics, monitoring and metrics that an orchestrator and controller can collect from each of the edge and gateway devices. For example, enterprise IT has easy visibility to anomalies in application usage and use of unsanctioned applications, then can easily adjust security policies as necessary. The enterprise can apply policies around specific applications, such as disallowing certain traffic or routing it through a firewall or a secure web gateway. What’s more, traffic steering and segmentation can help meet regulatory or internal compliance requirements.
Conclusion
Security is a top priority for any networking architecture—especially as enterprises move more applications to the cloud. A flexible cloud delivered SD-WAN solution that can address on premise needs as well as cloud-centric needs, or a combination of both, can offer a full range of capabilities on the security checklist and provide a more secure architecture than a traditional WAN.